
Five simple habits that stop a shocking amount of cyber trouble.
Here is the part that should make every business owner pause for a second.
The Change Healthcare breach in 2024 — the one that disrupted prescription processing and caused chaos across the healthcare system — started with an account that did not have multi-factor authentication turned on.1 One login. One missing safety step. That was enough.
That is the weird thing about cybersecurity. The stories sound dramatic. Hackers. Ransomware. Dark web. Emergency meetings. But the thing that could have stopped the mess is often painfully ordinary.
This is not movie-hacker stuff. This is front-door stuff. And a lot of businesses are still leaving the front door wide open.
So let’s talk about the five boring security moves that do a lot of heavy lifting.

MFA is the extra step after your password. You log in, your phone asks you to approve it, and then you move on with your day.
Mildly annoying? Sometimes. Worth it? Absolutely.
Microsoft has said MFA can block more than 99.9 percent of account-compromise attacks.2 That is about as close to a no-brainer as cybersecurity gets.
The problem is that a lot of small businesses still have not turned it on. A Cyber Readiness Institute study found that 65 percent of small and medium businesses do not use MFA and do not plan to implement it soon.3
That is wild because stolen passwords are everywhere. Attackers do not need to break into your building. They just need one reused password from one old breach and an account with no second step.
Where to start: Turn MFA on for email first. Then accounting. Then banking. Then your CRM, admin portals, cloud apps, and anything else that would ruin your week if the wrong person got in.

Software updates are easy to put off because they always show up at the worst possible time.
You are busy. You click later. Then later becomes next week. Then next week becomes “I thought someone else handled that.”
Attackers love that.
When a serious vulnerability becomes public, the clock starts ticking. In 2025, AWS reported active exploitation attempts against the React2Shell vulnerability within hours of public disclosure.4
That is how fast this moves now.
The update is not just a new button color or a bug fix for some feature you never use. Sometimes it is the lock for a door that everyone on the internet now knows exists.
You do not have to be perfect. You just do not want to be the easiest target in the room.

A backup that has never been tested is not a backup.
It is a hopeful thought.
Ransomware gangs know businesses rely on backups, so they often look for those backups first. They try to delete them, encrypt them, or make them useless before the real damage begins.
That is why a good backup plan is not just “we have backups.” A real plan means:
Because the worst time to learn your backup failed is right after every shared folder in the company turns into ransom notes.
The goal is simple. When something bad happens, you want to say, “That was ugly, but we can restore.” Not, “Does anyone know where the backup password is?”
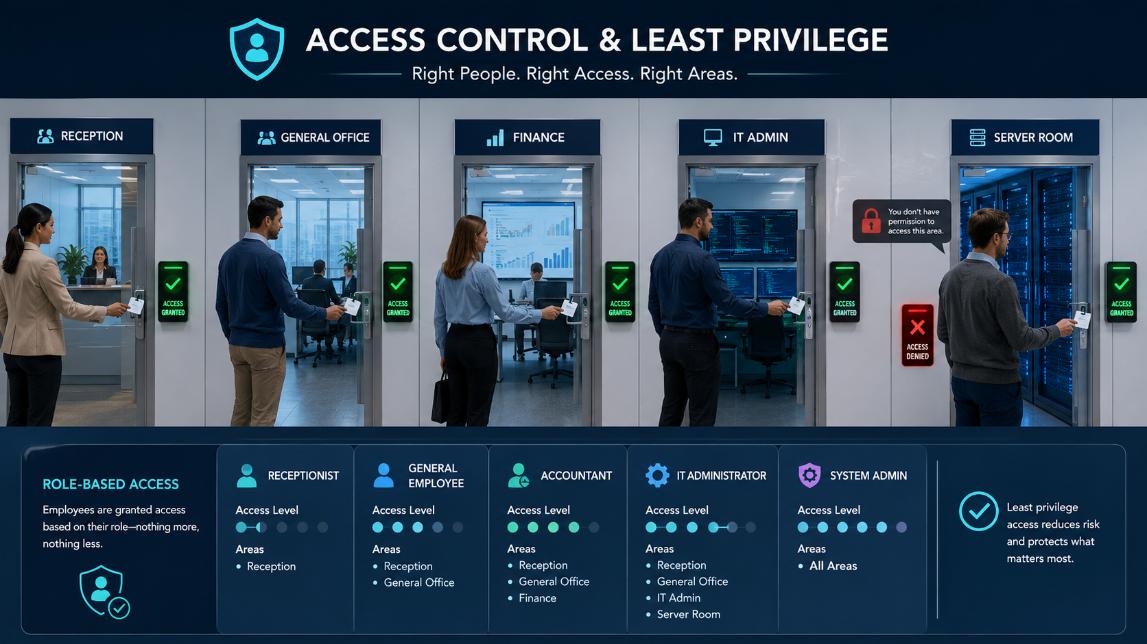
A lot of businesses are too generous with access.
Someone needs one folder, they get the whole drive. Someone needs one admin function, they get full admin rights. Someone leaves the company, and their account quietly lives on like a ghost in the machine.
That is how small problems become big ones. If a basic user account gets compromised, that is bad. If an admin account gets compromised, that can be catastrophic.
The rule is simple. People should only have access to what they need to do their job. Nothing extra. Nothing “just in case.” Nothing left over from an old role three years ago.
Do an access review and you will almost always find surprises:
This is not glamorous work, but it is exactly the kind of cleanup that keeps a bad login from turning into a full-blown disaster.
Because they are.
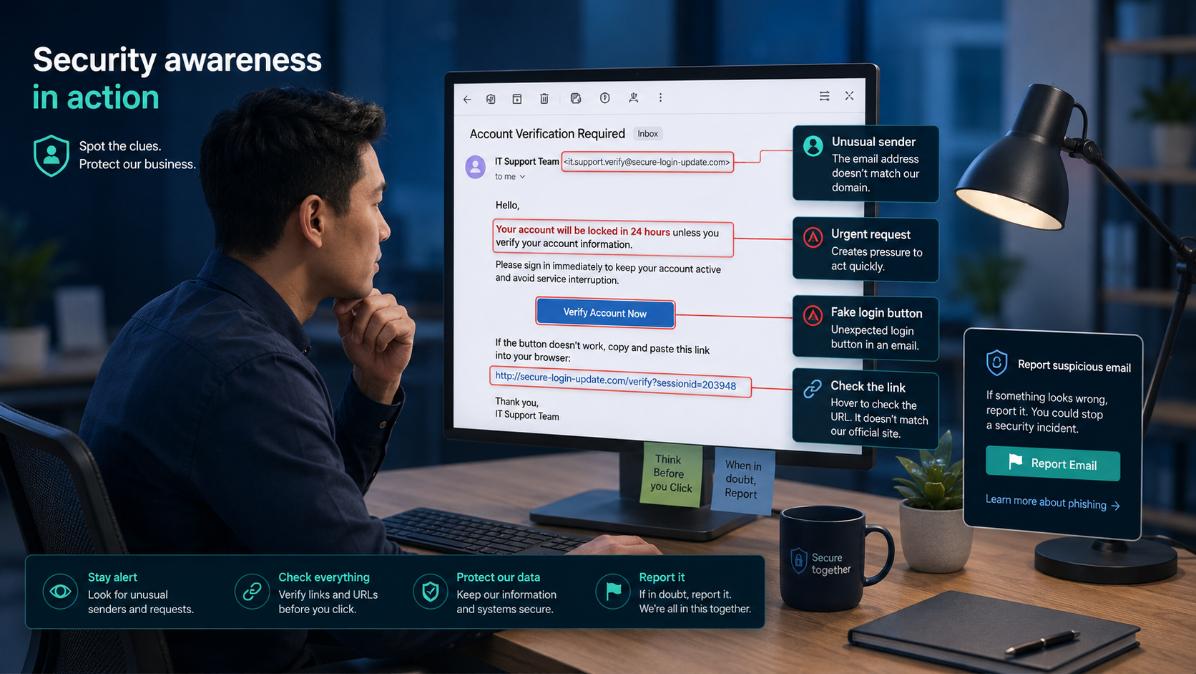
Phishing emails are not as obvious as they used to be. The old scams had weird grammar, broken logos, and a sender address that looked like it came from a vending machine.
Now they can look like your bank. Your vendor. Your payroll company. Your boss asking for something that sounds just normal enough to click.
The answer is not to treat employees like they are the problem. The answer is to train them like they are part of the defense.
Give them realistic examples. Run simple phishing tests. Make it easy to report something suspicious. Do not create a culture where people hide mistakes because they are afraid of getting yelled at.
A fast report can save the whole company a massive headache.
Security training should not feel like a punishment. It should feel like giving people the radar they need to spot the weird stuff before it turns into expensive stuff.

None of this is magic.
MFA. Updates. Backups. Access control. Training.
That is the boring list.
But boring is good. Boring means fewer emergencies. Fewer panic calls. Fewer locked files. Fewer awkward conversations with customers. Fewer reasons to wonder whether the business is about to show up in a breach report.
The average cost of a data breach hit $4.88 million in IBM’s 2024 report.5 Most small businesses do not need enterprise complexity to reduce their risk. They need the fundamentals done correctly and checked consistently.
That is where RockIT Solutions comes in. We help small businesses and veteran-owned businesses in the St. Augustine area get the basics right before the basics become a crisis.
No scare tactics. No jargon. No bloated security stack you do not need. Just practical protection that makes sense for how real businesses actually operate.
Share a few details and our team will follow up with the next best step.